Search Results for: computer security
-
Networking+

VIRTUALIZATION AND DISTRIBUTED COMPUTING
Virtualization and distributed computing have revolutionized the computing world, bringing the wholesale changes to the applications, services, system data, and…
Read More » -
Security+

Types of Biometric Controls
There are a number of biometric controls that are used today; below we have the major implementations and their specific…
Read More » -
Mobile
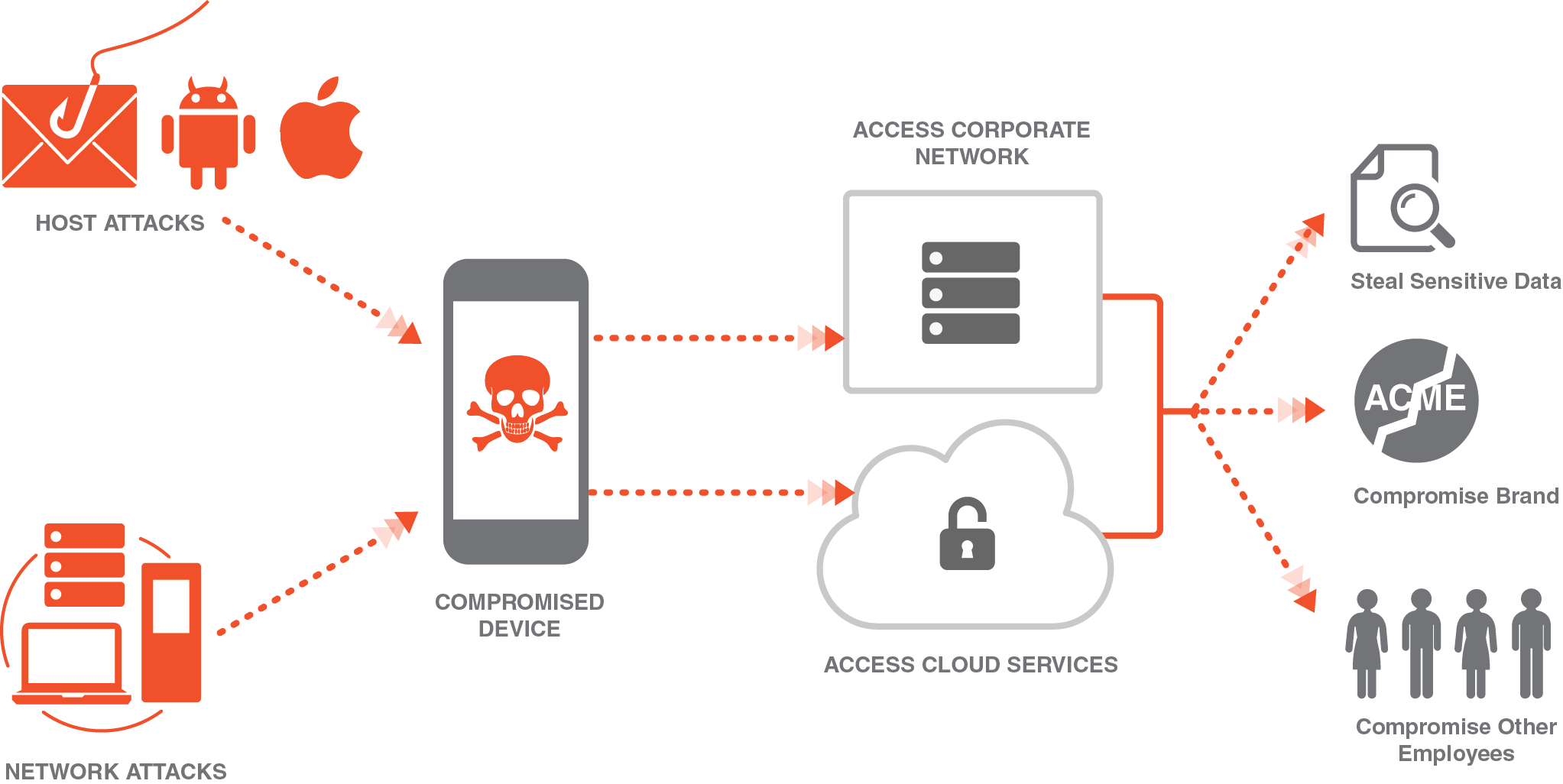
MOBILE DEVICE ATTACKS
A recent information security challenges is the number of mobile devices ranging from USB flash drives to laptops that are…
Read More » -
Black Hat
Types of Attackers
Controlling access is not limited to the control of authorized users; it also includes preventing unauthorized access. Information systems may…
Read More » -
Security News

Firefox Is Back. It’s Time to Give It a Try.
Have you ever felt that the web is breaking? When you are shopping for toaster oven, you can expect an…
Read More » -
Security+
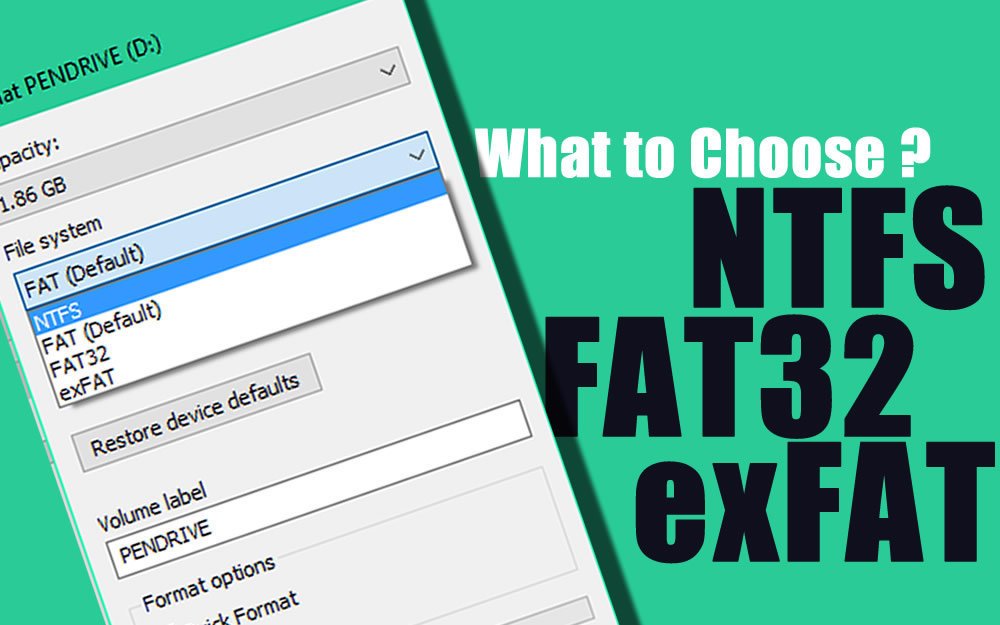
File Systems
File Systems: Several filesystems are involved in the operating systems, and from a network perspective, they have a high level…
Read More » -
Notes

Types of Hardware Tools
Hardware Tools: So which hardware-based tools should you become fluent with or concentrate on when testing or training? Becoming familiar…
Read More » -
Security News

Smart Watches & Fitness Trackers Can Spy ATM PIN and Unlock Smart Phones
Smart Watches and Fitness Trackers: IoT has extends the connectivity of physical devices beyond the standard devices, it affects the…
Read More » -
Black Hat
Understanding Denial of Service
Understanding DoS: Denial of Service is an attack that aims at preventing normal communication with a resource by disabling the…
Read More »