Techie Talks
-
Black Hat

Ways to Locate Wireless Networks
Ways to Locate Wireless Networks: In order to attack, you must first find a target, and though site surveys can…
Read More » -
Black Hat

USB Password Theft
USB Password Theft: In contrast to manual methods, there is some automated mechanism for obtaining passwords, such as via USB…
Read More » -
Black Hat
Performing a Password Crack – Insecure Logon Systems
Insecure Logon Systems: Many web applications require some sort of authentication or login process prior to their use. Because of…
Read More » -
Wi-Fi Hacking

Cracking WPA with Reaver and Wash
Cracking WPA: To crack WPA you must use a different approach than you would with WEP. Fortunately, one of the…
Read More » -
Wi-Fi Hacking

Cracking WEP with Kali Linux
Cracking WEP with Kali Linux: In this exercise you will use Kali Linux 2.0 to break WEP. To perform this…
Read More » -
Cloud
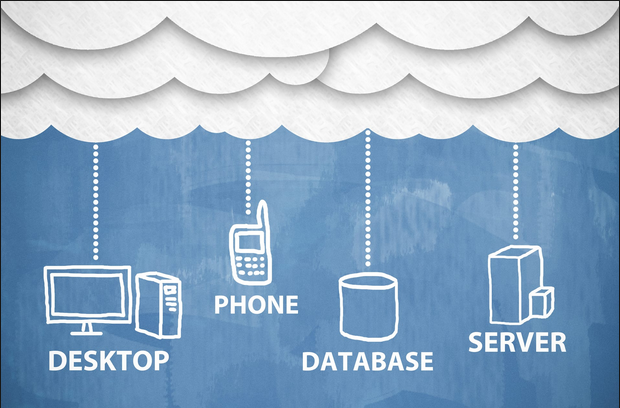
Types of Cloud Solutions
Types of Cloud Solutions: Calling the Cloud “the cloud” simply isn’t accurate because it doesn’t fully describe the scope of…
Read More » -
Cloud
What is the Cloud Technologies and Security
What is the cloud: While cloud computing is new term, it is not a new concept and is actually a…
Read More » -
Mobile

Mobile Device Security – Countermeasures – Summary – Exam Essentials
Countermeasures: Similarly to securing desktops, servers, networks, and other equipment, you can take some basics steps to make mobile devices…
Read More » -
Mobile

Penetration Testing Mobile Devices Using Android
Penetration Testing Mobile Devices: So how do we pen test mobile devices? In many ways the process is similar to…
Read More »
