UNDERSTANDING CYBER SECURITY – Download Free Hacking Books
1.Backgrounding-
- A. networking technologies (e.g., hardware, infrastructure)
- web technologies (e.g., web 2.0, skype)
- systems technologies
- communication protocols
- malware operations
- mobile technologies (e.g., smart phones)
- telecommunication technologies
- backups and archiving (e.g., local, network)
2.Analysis/Assessment-
- A. data analysis
- systems analysis
- risk assessments
- technical assessment methods
- Security-
- systems security controls 25% 31
- application/file server
- firewalls
- cryptography
- network security
- physical security
- threat modeling
- verification procedures (e.g., false positive/negative validation)
- social engineering (human factors manipulation)
- vulnerability s canners
- security policy implications
- privacy/confidentiality (with regard to engagement)
- biometrics
- wireless access technology (e.g., networking, RFID, Bluetooth)
- trusted networks
- vulnerabilities
- Tools / Systems / Programs-
- network/host based intrusion
- network/wireless sniffers (e.g., WireShark, Airsnort)
- access control mechanisms (e.g., smart cards)
- cryptography techniques (e.g., IPsec, SSL, PGP)
- programming languages (e.g. C++, Java, C#, C)
- scripting languages (e.g., PHP, Java script)
- boundary protection appliances
- network topologies
- subnetting
- port scanning (e.g., NMAP)
- domain name system (DNS)
- routers/modems/switches
- vulnerability scanner (e.g., Nessus, Retna)
- vulnerability management and protection systems (e.g., Foundstone, Ecora)
- operating environments (e.g., Linux, Windows, Mac)
- antivirus systems and programs
- log analysis tools
- security models
- exploitation tools
- database structures
- Procedures /Methodology-
- cryptography
- public key infrastructure (PKI)
- Security Architecture (SA)
- Service Oriented Architecture
- information security incident
- N-tier application design
- TCP/IP networking (e.g., network routing)
- security testing methodology
- Regulation/Policy-
- security policies
- compliance regulations (e.g., PCI)
- Ethics-
- professional code of conduct
- appropriateness of hacking
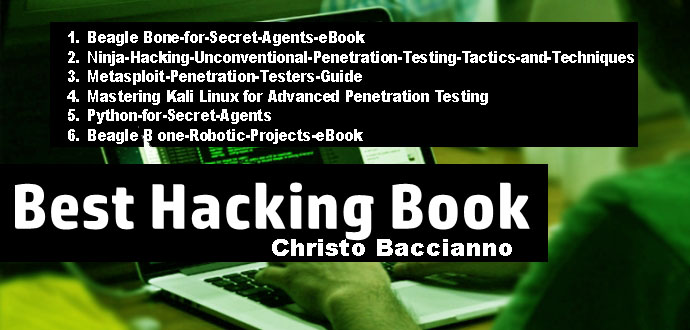
Few Books that will probably will help you to be master as Professional Ethical Hacker
- Beagle Bone-for-Secret-Agents-eBook (Click To Download)
- Ninja-Hacking-Unconventional-Penetration-Testing-Tactics-and-Techniques (Click To Download)
- Metasploit-Penetration-Testers-Guide (Click To Download)
- Mastering Kali Linux for Advanced Penetration Testing (Click To Download)
- Python-for-Secret-Agents (Click To Download)
- Beagle B one-Robotic-Projects-eBook (Click To Download)
I can also teach you each part of every step to become a professional. Each one must be understood to be able to audit/pentest a network.
All rights reserved to the author of this books and if you like their books please support the authors to purchase from them. And all the books stuff etc are provided here by Christo Baccianno | STEPS FOR UNDERSTANDING CYBER SECURITY – Download Free Hacking Books



One Comment