Search Results for: computer security
-
Web Hacking
Extracting Information From DNS
Extracting Information from DNS: DNS servers are an excellent target for hackers and penetration testers. They usually contain information that…
Read More » -
Security+
The Early Days of Hacking
The Early Days of Hacking: The idea of hacking and hackers goes way back to the first technologies enthusiastic that…
Read More » -
Security+

Biometrics: Installing Biometric Devices
Biometrics: Biometrics systems use some kind of unique biological trait to identify a person, such as fingerprint, patterns on the…
Read More » -
Security+
Smart Cards
Smart Cards are generally used for access control and security purposes. The card itself usually contains a small amount of…
Read More » -
Security+

ACL: Access Control Lists
Access Control Lists: Related to permissions is the concept of the access control lists (ACL). An ACL is literally a…
Read More » -
Security+

Databases and Technology
Databases & Technology: One key reason why computers are installed is for their ability to store, access, and modify data.…
Read More » -
Networking+
Understanding Wireless Devices
Wireless Devices: Mobile devices, including Smartphones, e-book readers, and tablet computers, are popular. Many of these devices use either RF…
Read More » -
Mobile

Penetration Testing Mobile Devices Using Android
Penetration Testing Mobile Devices: So how do we pen test mobile devices? In many ways the process is similar to…
Read More » -
Security+
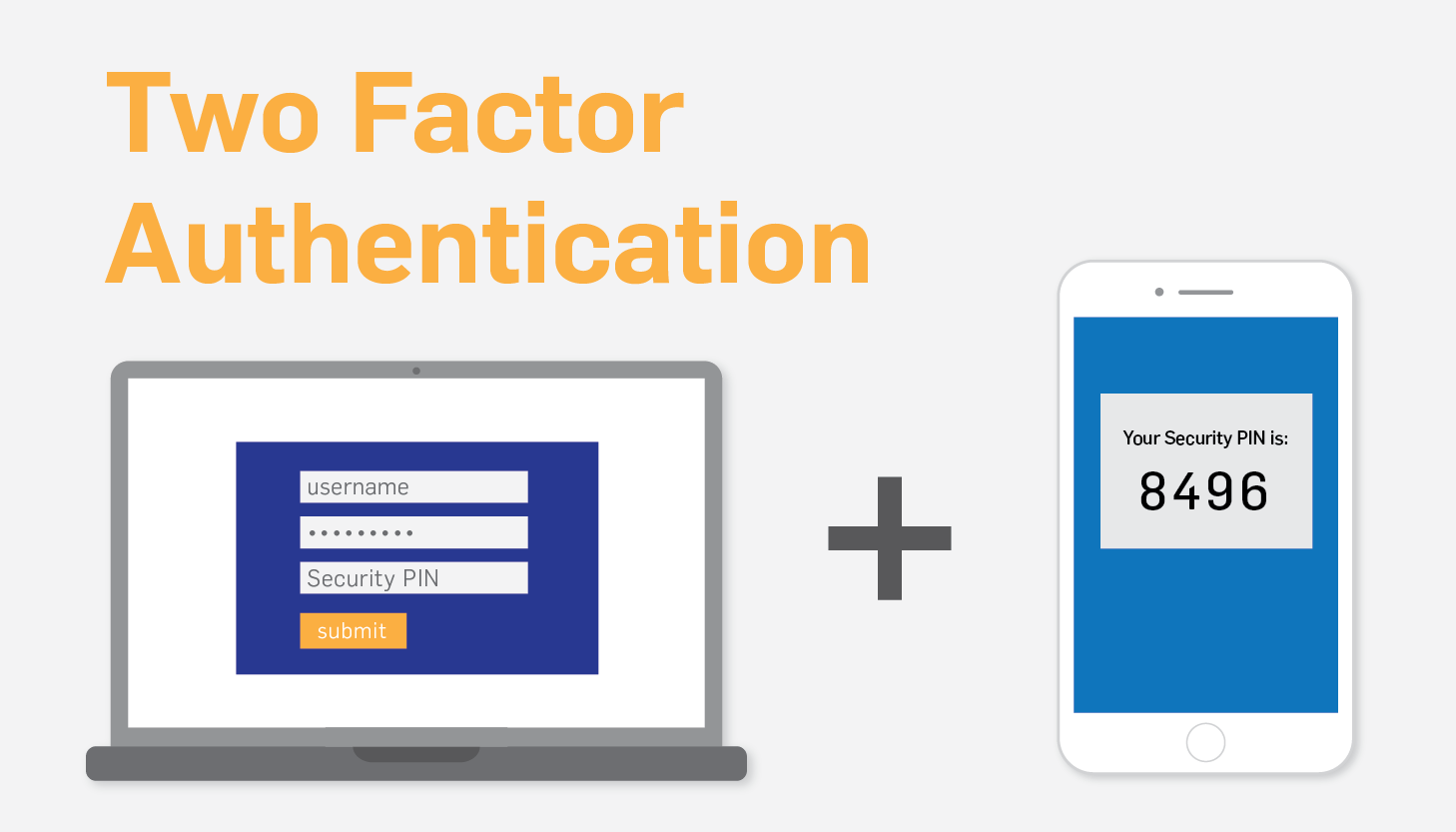
Authentication (Single Factor) and Authorization
Authentication (Single Factor) and Authorization: The most basic form of authentication is known as single-factor authentication (SFA), because only one…
Read More » -
Nmap
USING NMAP TO PERFORM A TCP CONNECT SCAN
USING NMAP TO PERFORM A TCP CONNECT SCAN USING NMAP TO PERFORM A TCP CONNECT SCAN: The first scan we…
Read More »