
Weak Passwords Let a Hacker Access Internal Sprint Staff Portal
Weak Passwords Let a Hacker Access Internal Sprint Staff Portal: It’s not for sure a great week for cell carriers. EE was hit with two security bugs and T-Mobile admitted a data breach. Now, Sprint is the recent latest phone giant who also admit a security lapse.
Using two sets of weak, this is easy-to-guess usernames and passwords, a security researcher who accessed an internal Sprint staff portal. It’s because the portal’s login page that did not use the two-factor authentication, the researcher — who did not want to be named — navigated to pages that could have allowed the access for customer account data.
Sprint is of course the fourth largest US cell network with over 55 million customers.
The TechCrunch who passed the details with screenshots of the issue to Sprint, which do confirmed the findings in the email.
“After looking into this, we do not believe customer information can be obtained without a successful authentication to the site,’ said a Sprint spokesperson.
“Based on the information and screenshots provided, legitimate credentials were utilized to access the site. Regardless, the security of our customer is a top priority, and our team is working diligently to research this issue and immediately changed the passwords associated with these accounts, the spokesperson said.
The very first set of these credentials let the researcher get into access of Sprint employee portal which allowed him to access the Sprint customer data — as well as the Boost Mobile and Virgin Mobile, which are Sprint subsidiaries. The researcher has also used another set of credential that allow him to access the part of website, which he said gave him an access to a portal for customer account data.
A screenshot that was shared with TechCrunch showed clearly that anyone with an access to this portal allowed the user to conduct a device swap, change the plans and add-ons, replenish a customer’s account, check activation status and view customer account information.
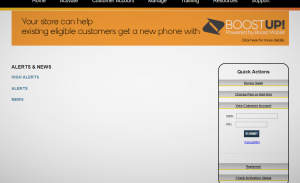
A screenshot showing an internal customer portal.
All the user who would need a customer’s mobile phone number and four-digit PIN number, that can be bypassed by cycling through every possible combination.
The researcher has also said that there are no limits on the number of PIN attempts.
Account PIN number that are highly sensitive which can be used to transfer the ownership from one person to another. That for sure can give an attacker easier pathway to carry out a “SIM Swapping” attack, which can easily target and hijack the cell phone numbers. Hackers who uses a mix of techniques — such as the calling up customer service and impersonating a customer, all the way to recruiting telecom employees to hijack SIM cards from the inside. In hijacking the phone number, the attackers can easily break into online account to steal the Instagram usernames, and intercept codes for two-factor authentication to steal the contents of cryptocurrency wallets.
SIM swapping is becoming big, albeit illegal business. An investigation by Motherboard that revealed that hundreds of people around the US have had their cell phone number stolen over the past few years.
But the authorities are now catching up to the growing threat of SIM swapping. Three SIM swappers have been arrested in the past few weeks alone.

![Bykea Had Publicly Exposed 400+ Million Users Data Including [CNIC, Address, License] ETC](https://www.techietalks.online/wp-content/uploads/2021/02/Bykea-Data-Breached.png)

